HOUSTON — Mass surveillance programs operated by an alphabet soup of three- and four-letter government agencies are an undeniable fact in today’s post-Snowden era. Whether or not most Americans are aware of the wide-ranging surveillance programs is another question, but the fact remains that the U.S. government has been monitoring communications in the United States and abroad for at least two decades.
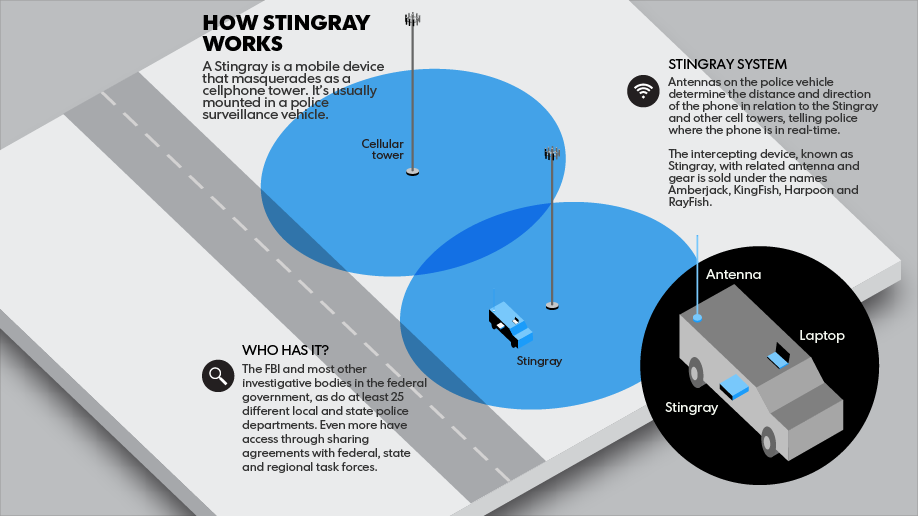
While past efforts typically involved federal government agencies, a new generation of products known as cell site simulators are being used by a growing number of local police departments and federal agencies. The most popular brand of simulators is made by the Florida-based Harris Corporation and sold under the brandname “Stingray” or “Stingray II.” Newer models are also being sold under the name Hailstorm.
Reports about Stingrays first began to surface in 2011, but details on the devices have only recently been revealed to the public. Just last month, a New York Supreme Court judge ruled that the Erie County Sheriff’s Office must comply with public records requests regarding the devices. The ACLU of New York sued the Sheriff’s Office after it failed to respond to requests for information on how the devices are used. Justice Patrick NeMoyer sided with the NYCLU and ruled that the Sheriff’s Office must hand over the data. NYCLU Staff Attorney Mariko Hirose, lead counsel on the case, said the decision “confirmed that law enforcement cannot hide behind a shroud of secrecy while it is invading the privacy of those it has sworn to protect and serve.”
The documents released by the Erie County Sheriff’s Office earlier this month include purchase orders, a letter from Harris Corp., a confidentiality agreement between the Sheriff’s Office and the FBI, a procedural manual, and summary reports of instances in which the device was used. The records show the department used the device 47 times from 2010 to 2014, obtaining a court order just once. This contradicts the department’s previous assurances that it would always obtain a court order or warrant to use the device.
The documents also highlight problems with non-disclosure agreements (NDAs) between the FBI and police, which often explicitly forbid police from discussing Stingrays in court orders unless given the specific written consent of the FBI.
What is a Stingray?
According to the Electronic Frontier Foundation:
“The Stingray is a brand name of an IMSI [international mobile subscriber identity] catcher targeted and sold to law enforcement. A Stingray works by masquerading as a cell phone tower—to which your mobile phone sends signals to every 7 to 15 seconds whether you are on a call or not— and tricks your phone into connecting to it. As a result, the government can figure out who, when and to where you are calling, the precise location of every device within the range, and with some devices, even capture the content of your conversations.”
It is not known whether the data is being stored, and if so, for how long and which agencies have access to it. Few of the device’s capabilities are acknowledged by law enforcement, but how it works is fairly well-known: As long as a cellphone is emitting a signal to a cell tower, a Stingray can find it. It has also been revealed that Stingrays force cellphones to send data back to the device “at full signal, consuming battery faster.” Thus, a constantly dying battery could be a sign that a user is being tracked.
 This undated handout photo provided by the U.S. Patent and Trademark Office shows the StingRay II, manufactured by Harris Corporation, of Melbourne, Fla., a cellular site simulator used for surveillance purposes. A police officer testified Wednesday, April 8, 2015, that the Baltimore Police Department has used Hailstorm, a upgraded version of the StringRay surveillance device, 4,300 times and believes it is under orders by the U.S. government to withhold evidence from criminal trials and ignore subpoenas in cases where the device is used.
This undated handout photo provided by the U.S. Patent and Trademark Office shows the StingRay II, manufactured by Harris Corporation, of Melbourne, Fla., a cellular site simulator used for surveillance purposes. A police officer testified Wednesday, April 8, 2015, that the Baltimore Police Department has used Hailstorm, a upgraded version of the StringRay surveillance device, 4,300 times and believes it is under orders by the U.S. government to withhold evidence from criminal trials and ignore subpoenas in cases where the device is used.
The devices can be handheld or vehicle-based, and “body-worn” Stingrays have also been developed, according to 2013 reports. It has also been reported that the U.S. Marshals Service has been working with the CIA to use a version of the cell site simulators, known as DRT boxes, inside Cessna planes. The so-called “Dirtboxes” are supposed to be used for criminal investigations, but the ACLU alleges they can collect data from tens of thousands of people on each flight. The civil liberties group filed a Freedom of Information Act (FOIA) request in November regarding the recently exposed program that uses aircraft to gather cellphone data.
Yet the major difference between any past programs and the Stingrays is the layers of secrecy involved with the use of the Stingray.
The first layer of secrecy is the use of NDAs by the Harris Corp. Local police departments have become subordinate to Harris and are prohibited from speaking on the details of their arrangements — even in court. The work of intrepid journalists and privacy advocates has led to the release of certain details regarding the NDAs.
An NDA signed by police in Tucson, Arizona, was exposed by public records requests from journalist Mohamad Ali “Beau” Hodai. Hodai, and his online news publication DBA Press, was able to obtain a copy of the contract signed by the Tucson police and Harris Corp. in 2010.
In an email from October 2013, also obtained by Hodai, Harris Corp.’s contract manager discusses his request with Tucson Police Department Sgt. Kevin Hall. The manager instructs Hall to redact or withhold the request, even giving the officer the specific laws to cite in the department’s response. In a complaint filed on behalf of Hodai in March 2014, the ACLU of Arizona said the TPD and the City of Tucson, “have allowed Harris Corporation to dictate the City of Tucson’s and TPD’s compliance with Arizona public records law.”
Similar cases have appeared in Florida and Baltimore. Authorities in Florida were tracking a suspected rapist using a Stingray. Court records show that police did not want to obtain a search warrant because they did not want to reveal information about the technology they used to track the suspect’s cellphone signal. In the Florida case, Det. Christopher Corbitt was mentioned as the officer who handles electronic surveillance programs. In a transcript of the closed court hearing in 2010 Corbitt told the court that the officers used the Stingray to locate the suspect in an apartment complex. Corbitt describes how the officers went door-to-door searching for a response from the suspect’s phone:
“We were able to actually basically stand at every door and every window in that complex and determine, with relative certainty . . . the particular area of the apartment that that handset was emanating from.”
More recently, Det. John L. Haley was questioned in November on the possible use of Stingrays in a Baltimore circuit court. Haley, who heads up Baltimore’s phone tracking unit, declined to answer any questions, citing an NDA with the FBI. Baltimore Circuit Judge Barry G. Williams reminded Haley he did not have an NDA with the court and threatened to hold the officer in contempt of court if he did not respond. The prosecution chose to withdraw the related evidence rather than discuss the technology any further.
Documents obtained by The Associated Press show the Baltimore Police Department is yet another local police department that complies with NDAs with the FBI. AP reported on April 9:
“The Baltimore police entered into an agreement with the Justice Department in 2011, which calls for the department to withhold information about the device in ‘press releases, court documents, during judicial hearings or during other public forums and proceedings.’ The agreement states that the department must seek FBI approval before sharing any details with other law enforcement agencies.”
It was also revealed that the BPD used the Stingray about 4,300 times since 2007, more than any other department in the country. The new information came in the testimony of Emmanuel Cabreja, a detective with the department’s advanced technical team. The officer said the police are using Hailstorm, an upgraded version of Stingray. Cabreja said he had used the Stingray about 600 to 800 times in the last two years alone.
The FBI and Harris Corp are both working to keep local police departments from disclosing new details about the technology. The FBI sent a letter to the Minnesota Bureau of Criminal Apprehension in 2012, ordering the department to contact the bureau if open records requests are filed. The letter says the department is to “immediately notify the FBI of any such request telephonically and in writing in order to allow sufficient time for the FBI to seek to prevent disclosure through appropriate channels.”
In another incredible exercise of federal authority, the U.S. Marshals intervened in a public records request to the Sarasota Police Department. The ACLU of Florida was seeking information on the technology when the group received a letter claiming that the records now belonged to the Marshals and could not be released.
Yet the FBI and Marshals are not the only federal agencies interested in keeping things quiet. According to Christopher Soghoian, the principal technologist at the ACLU, Harris Corp. is required to call the NSA if anyone calls the company inquiring about the use of the devices.
Victories in the fight for transparency
The New York State Supreme Court decision has not been the only victory in the fight for transparency and accountability.
Last month TheBlot magazine released the first official look at a 2010 Stingray user manual, obtained through FOIA requests to the FCC. The manual and other records reviewed by the magazine provide further detail. For example, one contract shows the U.S. Navy was one of the first groups to purchase the equipment from Harris Corp., which may help explain the aquatic nicknames.
“Sources familiar with Harris’ 2010 application told The Blot that the company had received authorization from the FCC several years before to manufacture and sell the devices specifically as an anti-terrorism tool, and that its application to the FCC’s Office of Engineering and Technology (OET) was intended to expand that authorization so that police could use legally use the devices beyond terrorism investigations.
The definition of what constituted an ‘emergency’ was intentionally left vague so that the authorization would cover law enforcement in a wide range of criminal investigations, the source said.”
The manual also shows that Stingrays and Kingfish technology are sold as part of a surveillance kit with third-party software and laptops. The laptops are manufactured by Dell and Panasonic, and the software designed by a cellphone forensics company called Pen-Link. The manual is filled with warnings and reminders that the information is “confidential” and “not for public inspection.”
Late last year, a judge ordered the release of documents related to the use of Stingrays in the state of Florida. In an application for a warrant, FBI Special Agent Michael A. Scimeca admitted that the devices have the potential to “intermittently disrupt cellular service to a small fraction” of wireless customers in the immediate area.
The surveillance device forces phones to downgrade from the 3G and 4G network to the less secure 2G network to intercept data being sent from the phones to cell towers. This can cause a disruption in Internet service and the ability to make and receive calls for a brief period of time. This news raises questions on what, if anything, the Federal Communications Commission, which is responsible for approving the device, knew about the service disruption.
In February, the Charlotte-Mecklenburg Police in North Carolina and local prosecutors were forced to release details about the secret surveillance program. The revelation followed an investigation by The Charlotte Observer and pressure from defense attorneys and privacy advocates, who feared police were unfairly targeting innocent bystanders with the technology.
The Observer reports that George Laughrun, a defense attorney in Charlotte, explained that due to the secrecy surrounding the technology and its use, it was difficult for judges and defense attorneys to protect the public against overreach by police.
“Judges probably didn’t understand” how the technology worked, Laughrun told the Observer. “I didn’t understand it. What is it? What does it do? What do you get from it?”
The CMPD will make changes to its program, including disclosing to judges exactly how they track cellphones and allowing those accused of crimes to learn whether police used a Stingray to arrest them. The Mecklenburg County District Attorney’s Office will also be releasing the results of a review of hundreds of criminal cases.
In at least one state, judges have started to require law enforcement agencies to specifically ask for permission to use the technology. The Tacoma News Tribune reported in November that Pierce County’s 22 Superior Court judges “require language in pen register applications that spells out police intend to use the device.” Pen register applications have typically been used to tap landline phones. Critics worry that in instances in which police do seek court approval they do so under the pen register and do not specifically tell the judges what device they are using and how it works. Indeed, the type of approval sought by police tends to vary from city to city and state to state.
 Defense attorneys have started filing motions asking prosecutors to disclose if defendants have been located by the use of cell site simulators or other tracking devices.
Defense attorneys have started filing motions asking prosecutors to disclose if defendants have been located by the use of cell site simulators or other tracking devices.
Meanwhile, several states are currently debating legislation that seeks to limit the use of Stingray surveillance. In California, the newly proposed California Electronic Communications Privacy Act would require warrants for the use of Stingray cellphone surveillance, also known as cell site simulators.
As the public wakes up to the dangers of indiscriminate monitoring, police departments are being forced to acknowledge and defend the programs. The Chicago Police Department has spent more than $120,000 in six months to fight a lawsuit filed by city resident Freddy Martinez, who says the department’s use of Stingray technology amounts to unlawful surveillance.
Concerns about the secrecy surrounding the use of Stingray technology have even reached the Senate. After questioning the Department of Justice about Stingrays on separate occasions last year, Sens. Patrick Leahy and Chuck Grassley stated that the department’s failure to answer their questions heightened their concern. Both Senators sent a new letter seeking answers from Attorney General Eric Holder last month.
Houston, we have a problem
While there may be some legitimate reasons for not releasing details about specific operations, the public has a right to know how police departments are using their tax dollars, especially when those tax dollars are funding devices with the capability to monitor the public.
The Houston Police Department has been using the tools since at least 2007, with upgrades in both 2012 and 2015. Earlier this month, the Houston City Council approved an allocation of $495,021 in funds for upgrades of the Stingray equipment and software — a decision which drew opposition from the city’s civil liberties advocates and activists. Houstonian Kevin Wambold told City Council, “We don’t need to spend half a million dollars on something police are unwilling to discuss.”
Despite the public approval of the updates and City Council records and purchase orders, Houston Police Chief Charles McClelland continues to deny that the department uses the technology while also insisting that appropriate constitutional measures are adhered to whenever surveillance technology is used.
“When it comes to any type of electronic evidence, since I have been police chief, the Houston Police’s policy is to get a warrant,” McClelland told MintPress News.
Based on the level of secrecy surrounding use of the tools, including NDAs with the FBI and Harris Corp., there is reason to suspect that the police chief might not be revealing everything he knows about Stingrays.
“As the President of the largest criminal defense bar in the country this surprises me, because to my knowledge no lawyer in Texas has ever seen anything filed requesting Stingray technology in any case,” Carmen Roe, president of Harris County Criminal Lawyers Association, said to MintPress.
Texas does not currently require law enforcement to obtain a probable cause warrant to use a Stingray. Gregory Foster, of the Electronic Frontier Foundation in Austin, Texas, believes this is part of the problem. “The law needs to be updated this session to establish a clear, unambiguous standard of a Constitutionally-valid probable cause warrant for Texas law enforcement use of Stingrays,” Foster told MintPress. Texas state lawmakers have introduced House Bill 3165 and Senate Bill 942, both of which would require warrants for cell site simulators.
Sgt. John D. Shirley, a retired investigator with the Houston Police, told MintPress the procedure for using a Stingray “was very streamlined” in his experience, but he did note that the process for obtaining a warrant was different than standard operating procedure. He explained:
“My experience with the Stingray devices was in 2009, when trying to track down a murder suspect. I made the request to a unit in CID [Communications Intelligence Unit] and they handled all the issues with obtaining the warrant. This was very different from the normal warrant process because I had no idea what information the warrant actually contained and I wasn’t the affiant to the warrant. This means that although I was directly involved in developing the probable cause and executing the warrant I was not at all involved in documenting the probable cause for the warrant.”
A source within HPD’s Criminal Intelligence Division told MintPress the unit that handles Stingray equipment for Houston is known as the Communications Intelligence Unit and consists of about five officers. These five officers handle incoming requests for use of the technology and, as Shirley highlights, they take care of any probable cause warrants, largely leaving the officers in the dark about the Stingray approval process.
Shirley says if Chief McClelland and Houston’s Mayor Annise Parker are sure the program is constitutional then they “should not shy away from open and honest debate.”
Open Records requests seeking more information about the Communications Intelligence Unit and the Houston Police Department’s use of Stingrays have been denied. The outright denials and other tight-lipped responses from law enforcement will likely continue until the public demands answers.
Indeed, Sgt. Shirley offers a stark warning: “Our law-enforcement agencies aren’t secret police. So for them to think they can deploy this new technology without the watchful eye of the communities they serve is a very bad omen to what we should expect in the future.”