MINNEAPOLIS– Since launching in 2006, Wikileaks has reportedly released over 10 million documents, including controversial disclosures that have helped unravel war crimes, uncover corporate secrets and even brought to light explosive revelations stemming from Hillary Clinton’s most recent presidential run.
Despite facing widespread international denunciation, Wikileaks has remained faithful in blowing the whistle on information that would have remained hidden from the public. These secrets have helped to expose many layers of the global state security apparatus and aided in shaping the discourse surrounding government and corporate transparency.
On April 7, Wikileaks released 27 documents from the CIA’s Grasshopper framework, a platform used by the agency to infect electronic devices such as phones, computers, and televisions for surveillance purposes. This information dump was part of a series known as “Vault 7,” which targets the agency’s covert hacking program. “This extraordinary collection,” Wikileaks writes, “which amounts to more than several hundred million lines of code, gives its possessor the entire hacking capacity of the CIA.”
According to the documents provided by Wikileaks, knowledge of the CIA’s invasive surveillance tools wasn’t confined to the agency, or even the National Security Agency. In fact, the details of these exploits were bought and shared by Britain’s Government Communications Headquarters, as well as other intelligence agencies.
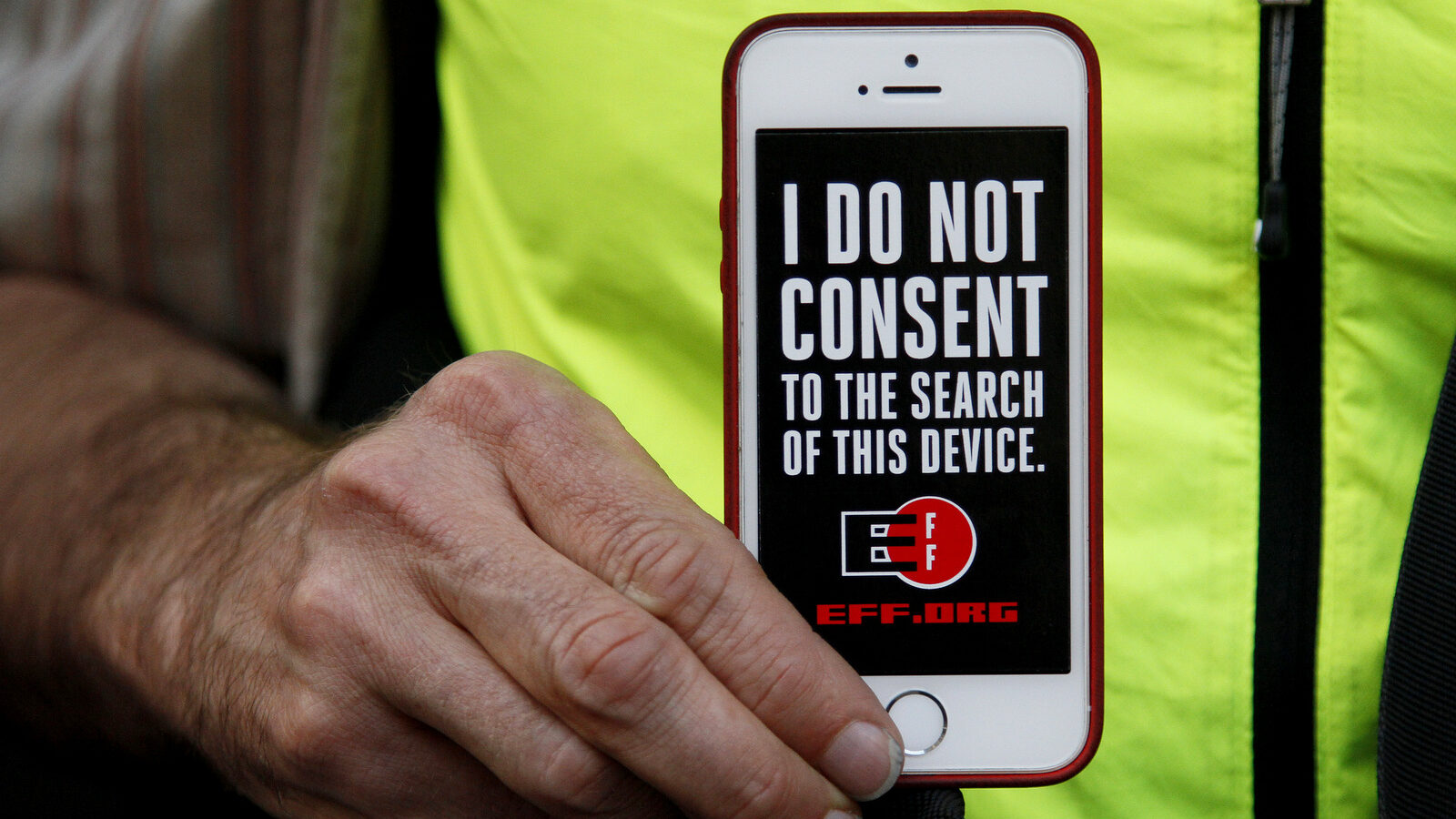
So what tools does the CIA have in its surveillance arsenal? Over 8,000 documents found in the “Vault 7” series reveal weaponized malware, trojans and viruses that could be used to spy on both domestic and foreign entities, impacting a variety of seemingly harmless household devices. Apple iPhones, Windows PCs and even Samsung TV sets can be used to conduct surveillance on anyone the CIA chooses to spy on. For example, one program named “Weeping Angel” details methods that can be used to hijack a Samsung F8000 TV in order to make it appear to be off when it is actually powered on.
The claim that your TV could be used to spy on you is no longer one of conspiracy. It is now our reality. “By hiding these security flaws from manufacturers like Apple and Google, the CIA ensures that it can hack everyone, at the expense of leaving everyone hackable,” WikiLeaks says. And these, by all accounts, are just the tip of the iceberg.
The “Vault 7” series, which has been described as being the largest leak of its kind targeting the CIA, originated from an “isolated, high-security network” within the CIA’s Center for Cyber Intelligence. The documents it contains were revealed to Wikileaks by way of an undisclosed source, though they’ve noted that their source could be a former U.S. government hacker or CIA contractor.
After the “Vault 7” series was first published, Trump administration spokesman Sean Spicer revealed the White House was concerned, and that “[a]nybody who leaks classified information will be held to the highest degree of law.” Despite these threats, WikiLeaks continues to release classified documents, showing us at least some of the secrets behind the CIA’s curtain.