
In 2008, then-Gov. Rod Blagojevich’s general counsel approved the covert purchase of a Stingray unit for the Illinois State Police. More than $240,000 in federal Homeland Security funds were used in the unit’s acquisition. Another $12,800 was spent to train four special agents on how to use the device at the Florida headquarters of Harris Corporation, the Stingray’s manufacturer.
This information was uncovered through a Freedom of Information Act request by a MuckRock user. It reflects a growing trend among law enforcement nationwide to use less-than-ethical means to conduct surveillance and tracking operations.
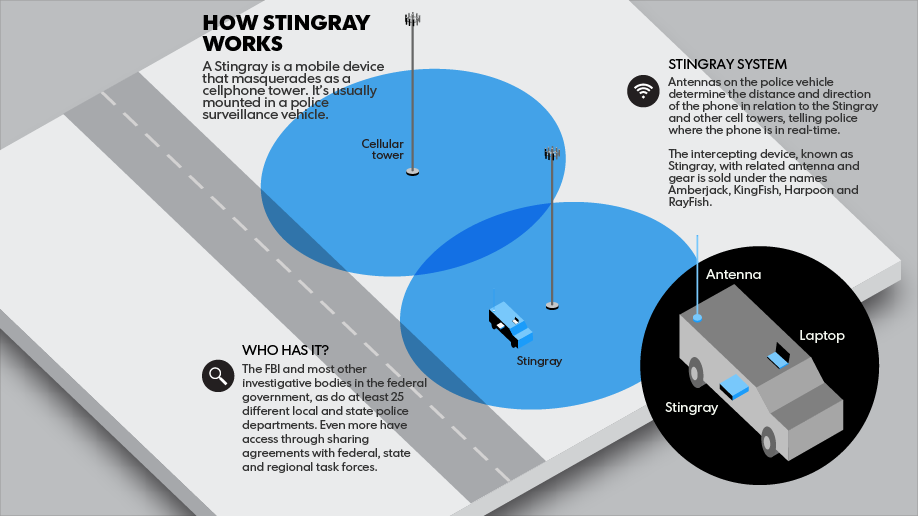
A Stingray is a mobile device that functions as an International Mobile Subscriber Identity-catcher, grabbing and recording user information from cellphones as they connect to mobile towers. As the cellular network does not require handset verification for GSM mobile phones, the Stingray — which basically works as a hacking device — masquerades as a base station, forcing cellphones to turn off their call encryption and capturing all of the IMSI data — including geolocation tags — of all GSM mobile devices in the area. According to agencies using the technology, it does not capture communication content.
In the United States, AT&T and T-Mobile use GSM networks, while Verizon Wireless, Sprint and U.S. Cellular use CDMA — which is not necessarily compatible with IMSI-catchers. Most wireless providers are currently upgrading their networks to be GSM-exclusive, however, and Verizon projects its network to be CDMA-free by the end of this year.
Though law enforcement are using Stingray devices in growing numbers, the device’s use in this regard presents a violation of civil liberties. It constitutes a warrantless search for those that are targeted, and since the technology catches all GSM mobile signals in a given area, it also captures the signals of innocent bystanders.
According to public records reviewed by USA Today and Gannett newspapers, of the more than 125 police agencies in 33 states reviewed, one in four have used a “tower dump,” or the complete download of a targeted mobile tower’s activity — including the identity, actions and location of every mobile device connected to that tower — over a set period of time. At least 25 possessed a Stingray, and 36 refused public records requests or questions concerning surveillance methodologies.
Some of the Stingrays were purchased using anti-terror grants allocated to the police departments by the Department of Homeland Security to supplement “War on Terror” actions and to assist in terrorism investigations. Others were borrowed from the U.S. Marshal Service.
As with many federal equipment acquisitions associated with the “War on Terror,” police agencies found a use for Stingrays in their regular work. Earlier this year, it was revealed that police in Tallahassee, Florida, had used IMSI-catchers more than 200 times since 2010 without obtaining warrants or court approval. After the American Civil Liberties Union published court information about the extensive use of the devices among Florida law enforcement, the Marshal Service seized the Stingray use records from the Sarasota Police Department to prevent disclosure to the ACLU.
While the courts have been inconsistent in their rulings, many argue that the question of unwarranted mass surveillance is complicated by the fact that there is a high level of secrecy surrounding the Stingray units and their application.
“The company would not answer questions about the systems, referring reporters to police agencies,” USA Today noted. “Most police aren’t talking, either, partly because Harris requires buyers to sign a non-disclosure agreement.”
Earlier this month, the ACLU of Florida released a set of police emails illustrating local police departments’ attempts to conceal Stingray use. In one email exchange, a Sarasota Police sergeant commented that in a warrant application, a North Port Police detective had “specifically outlined the investigative means used to locate the suspect.” In response, the sergeant requested that the detective submit a new probable cause warrant application that did not mention the Stingray.

“In the past, and at the request of the U.S. Marshalls [sic], the investigative means utilized to locate the suspect have not been revealed so that we may continue to utilize this technology without the knowledge of the criminal element. In reports or depositions we simply refer to the assistance as ‘received information from a confidential source regarding the location of the suspect.’ To date this has not been challenged … ,” wrote Sgt. Ken Castro in the 2009 email.
Taken as a whole, this situation reflects one in which instances involving the invasion of privacy and the corruption of civil protection go beyond the national security narrative. It also illustrates a wholesale redefinition of the demarcation between expectations of privacy and what constitutes public observation.
With no clear definitions of what constitutes the reasonable use of IMSI-catchers and tower dumps, potentially thousands of individuals are at risk of having their personal data caught and saved for investigations no more significant than a car break-in sting. This was the case in 2011, when Richmond County, South Carolina, Sheriff Leon Lott ordered four cell data dumps from two towers to ascertain who was responsible for a spree of break-ins that included his police-issued SUV.
“We’re not infringing on their rights,” Lott said in defense of his actions. “When they use that phone, they understand that information is going to go to a tower. We’re not taking that information and using it for any means whatsoever, unless they’re the bad guy or unless they’re the victim.”
Ultimately, the definitions of personal space and public space must be clarified. It is assumed that one’s privacy is sacred, but more than ever before, it is necessary to codify and enforce the point at which the individual’s public self ends and his private self begins.
“We have to be careful because Americans deserve an expectation of privacy, and the courts are mixed right now as to what is an expectation of privacy when using a cellphone,” U.S. Rep. Dennis Ross of Florida, an advocate for strengthened privacy laws, said last year. “More and more, we’re seeing an invasion of what we would expect to be private parts of our lives.”

