INSURGE INTELLIGENCE — On Monday 4th, the New York Times reported that the National Security Agency has “quietly” shut down a controversial phone records surveillance program revealed by whistleblower Edward Snowden in 2013.
The claim was made by a senior Republican congressional aide who told the newspaper that the Trump administration had stopped using the program, which analyses the domestic call and text logs of American citizens, due to technical problems.
On Twitter Snowden hailed the news as a “victory”, while Intercept journalist Glen Greenwald, who broke the Snowden story to international acclaim, took the story at face value. Neither of them raised the obvious question — is the “shut down” of this program merely a smokescreen to continue spying on American phones under new or different secretive programs?
Since then, further doubt was cast on the NYT report when NSA chief General Paul Nakasone refused to confirm or deny the story. But he did tell a major security conference on Wednesday that the agency was still “in a deliberative process” about whether to use a revamped version of the vast database of American phone records.
All of this, however, is an elaborate ruse. According to two former top NSA officials interviewed by INSURGE, there is no credible reason to believe that NSA phone surveillance has truly been shut down.
What shut down?
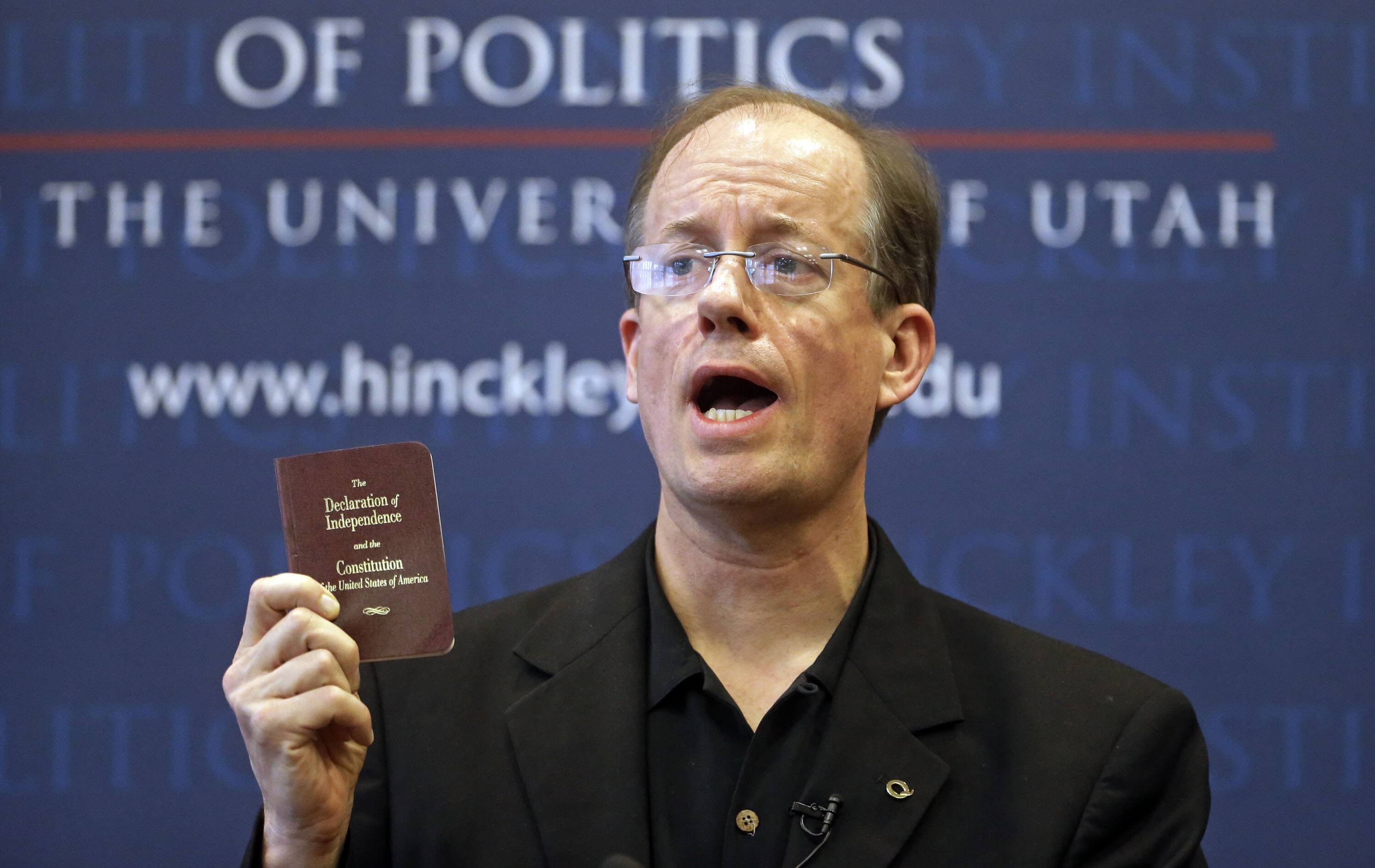
When the NYT story broke, I reached out to two former senior NSA officials, Russ Tice and Thomas Drake, to find out what they thought.
Both of them told me that the NSA’s shut down of this particular program did not imply an end to domestic phone record surveillance, but quite the opposite — that the program had been superseded by superior technology.
According to Russ Tice, a former senior NSA intelligence analyst who had previously worked with the US Air Force, Office of Naval Intelligence and Defense Intelligence Agency, the latest claim that the NSA was rolling up phone surveillance beggared belief.
“Why would anyone believe a bloody word of what NSA says about their mass domestic surveillance programs?” said Tice, who was the first NSA whistleblower who exposed unlawful surveillance and wiretaps of American citizens as early as May 2005. “They have lied repeatedly in the past and they are likely lying now. They have been collecting metadata and content, word-for-word, both voice and text, for some time now.”
I asked Tice how certain he was that the NSA was still conducting phone surveillance of Americans in the United States. “Of course NSA is still conducting phone and computer comms surveillance and yes, ‘wider programs’ go on and a new massive program that is more efficient is likely to have already been implemented,” he told me.
The real reason the current program has become defunct is that there is now better technology for more advanced surveillance.
If anything, they no longer need this particular program to parse the card catalog — meta data — and can mine the content data directly with enhanced algorithms and processing and strapping. And when there is no pushback capability, congress is at the mercy of NSA to inform them on NSA’s abuses.”
Hidden programs under secret interpretations of different laws
Thomas Drake, a former senior executive of the NSA who blew the whistle on illegal mass surveillance, waste and mismanagement at the agency several years before Snowden’s revelations, agreed that NSA phone surveillance “continues in other forms” in spite of the closure of this particular program.
Much has been made of the impending expiry of the USA Freedom Act of 2015, due this December, under which the current phone surveillance program is run. But Drake told me that the NSA simply doesn’t need the Freedom Act to authorize continued warrantless phone surveillance of American citizens in the homeland.
Surveillance can still continue, he said, “under yet other special, exigent, exceptional authorities and programs — including Section 702 and Executive Order 12333 — hiding in secret.”
Drake acknowledged that the NSA was also shifting toward adapting to widespread the changes in technology use, which could well have made the old program less than useful. “Communications using traditional land line and cell phone numbers and regular cellular text messaging is increasingly taken place on other messaging apps,” he added. “With respect to other authorities and cut outs, there are yet still other surveillance players and actors, too.”
In a series of tweets about the subject, Drake warned that the NSA’s recent history hardly vindicated the agency’s claims: “All these domestic spying programs fundamentally violated the Constitution, FISA & 4th Amendment on a mass scale, then went under cover of secret FISC approval, secret interpretations of law & then passage of unconstitutional ex post facto laws to make them ‘legal’.”
All these domestic spying programs fundamentally violated the Constitution, FISA & 4th Amendment on a mass scale, then went under cover of secret FISC approval, secret interpretations of law & then passage of unconstitutional ex post facto laws to make them ‘legal’.
— Thomas Drake (@Thomas_Drake1) March 6, 2019
Tice and Drake’s views corroborate an independent analysis by The Register, which observes that the association of the Freedom Act’s Section 215 program with phone metadata could be advantageous for the agency:
If the NSA offers to give up its phone metadata collection voluntarily, it opens up several opportunities for the agency. For one, it doesn’t have to explain what its secret legal interpretations of the law are and so can continue to use them. Second, it can repeat the same feat as in 2015 — give Congress the illusion of bringing the security services to heel. And third, it can continue to do exactly what it was doing while looking to everyone else that it has scaled back.
Here’s one thing we are sure of: the NSA has already figured out how to get all the information that was gathered through the metadata part of Section 215. It will be through a different law under a different secret legal interpretation.”
A history of subversion
According to Tice, illegal NSA surveillance was targeted across the federal government in order to secure political leverage. He describes this use of surveillance as a counter-democratic tool allowing the agency to pressure elected leaders across the House and Senate.
Between 2002 and 2005, he said, he discovered that the NSA had been targeting all communications of Congress, FISA, the Supreme Court, senior Pentagon officials, the media, and even future presidential prospects.
The NSA was essentially “collecting fodder for their lists of dirt for blackmailing all levels of top government officials”, said Tice. The idea was “to ensure they had leverage with those that could conduct oversight.”
But NSA surveillance extends far beyond this to offensive capabilities which remain undisclosed to this day.
Tice said that due to his role at the NSA, he was aware of a highly classified program of activity which has never been revealed before, concerning ‘Special Access Program (SAP) Offensive Information Warfare’.
SAP refers to what Tice describes as the “black world”, an arena of completely unaccountable projects to develop technologies with frightening reach and power. “These programs go very far beyond just collecting communications — they can reach out and touch you, and cause great, even grave, tangible harm.”
I am talking hardcore offense. The Title 10 and Title 50 restriction did not apply to my world. As I was once told at an after action briefing when I brought up some collateral damage we had caused, ‘We are above the laws and any form of oversight, we do a we please. So just chill out Russ’. I was thinking, holy shit, we are out of control. Then later I was even more horrified to realize he was correct, we had no controls on us.”
When I asked Tice to provide further detail on these offensive information warfare capabilities, he said that he declined to elaborate.
But he did emphasize that Snowden’s revelations on mass surveillance represent a tiny tip of the iceberg on what the NSA has been doing. He claims that a whole black world of secret programs exists, largely funded by the trillions of dollars that have gone missing from the US Department of Defense. These have gone to “black programs that are hidden, in many cases, from Congress.”
‘Ghost’ black programs
There are three different forms of SAP, Tice said: acknowledged, unacknowledged, and “Ghost” black programs. ‘Acknowledged’ programs are known to Congressional and Senate representatives sitting on the defense and intelligence committees.
In contrast, ‘unacknowledged’ black programs are known to a select number of representatives — the top majority and minority chairs and members in the defense and intelligence committees. On rare occasion, a single select member of the House might come to know by invitation only.
Then there are ‘Ghost’ black programs which the Pentagon and intelligence agencies “hide from all of Congress,” said Tice. “Many of these programs involved cutting edge technologies that are extremely expensive. I was an advanced technology analyst for many of these programs that included applications in space technology.”
During Tice’s tenure, these programs were only operational outside the United States. “The real question is whether the NSA has now begun to subject the citizens of the USA to their formidable black world offensive information warfare capabilities. There will be no recourse against Big Brother when it wields NSA’s weapons domestically against us all.”
Twelve years ago, Tice testified before the House Government Reform Subcommittee on National Security, Emerging Threats and International Relations. He told the committee that although the NSA’s Special Access Program might have violated the Constitutional rights of millions of American citizens, neither the committee members nor even the NSA inspector general had the necessary security clearances to be told about the programs, let alone reviewing them more formally.
Tice was scheduled to testify before the Senate Armed Services Committee a week later about a “different angle” of NSA surveillance, but this never happened. Tice said that at the time the Pentagon and NSA had “told Congress they could not talk to me because they did not have the proper security clearances.”
In short: don’t believe the chorus of headlines implying that the NSA is shutting down its bulk surveillance program. Far from it. The agency is merely evolving and recalibrating, and as usual, very few in the press, Congress and US government are asking the awkward questions that urgently need to be asked.
Top Photo | Employees work inside of the National Cybersecurity and Communications Integration Center during a media tour in Arlington, Virginia June 26, 2014. Kevin Lamarque | AP
Dr. Nafeez Ahmed is the founding editor of the 100% reader-funded investigative journalism project INSURGE intelligence. His latest book is Failing States, Collapsing Systems: BioPhysical Triggers of Political Violence (Springer, 2017). He is an 18-year investigative journalist, formerly of The Guardian where he reported on the geopolitics of social, economic and environmental crises. He now reports on ‘global system change’ for VICE’s Motherboard. He has bylines in The Times, Sunday Times, The Independent on Sunday, The Independent, The Scotsman, Sydney Morning Herald, The Age, Foreign Policy, The Atlantic, Quartz, New York Observer, The New Statesman, Prospect, Le Monde diplomatique, among other places. He has twice won the Project Censored Award for his investigative reporting; twice been featured in the Evening Standard’s top 1,000 list of most influential Londoners; and won the Naples Prize, Italy’s most prestigious literary award created by the President of the Republic. Nafeez is also a widely-published and cited interdisciplinary academic applying complex systems analysis to ecological and political violence. He is a Research Fellow at the Schumacher Institute.
Source | INSURGE intelligence


