Greenwald and Gallagher reported that after WikiLeaks was formed in 2008, the U.S. Army classified the organization as an enemy and “plotted how it could be destroyed.”
Greenwald and Gallagher reported that after WikiLeaks was formed in 2008, the U.S. Army classified the organization as an enemy and “plotted how it could be destroyed.”
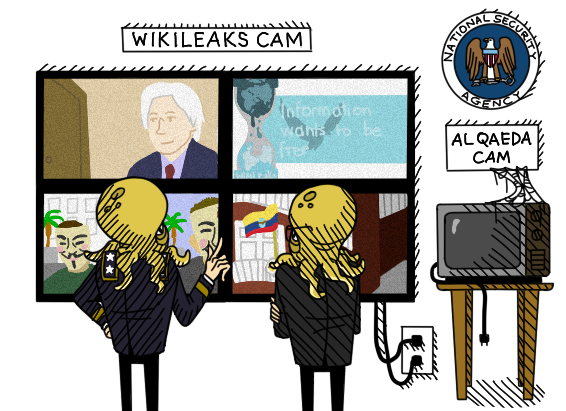
Greenwald and Gallagher reported that after WikiLeaks was formed in 2008, the U.S. Army classified the organization as an enemy and “plotted how it could be destroyed.”
The Guardian’s organized computer destruction represents just one chapter of a governmental “freak-out,” in which the British government was unprepared for its secrets to come out.

The Guardian’s organized computer destruction represents just one chapter of a governmental “freak-out,” in which the British government was unprepared for its secrets to come out.
In light of a growing choir of Julian Assanges and Edward Snowdens, the reality is that everyone has a right to be heard.
In light of a growing choir of Julian Assanges and Edward Snowdens, the reality is that everyone has a right to be heard.
“Reform” proposals designed to “make the system prettier and more politically palatable… while leaving the system fundamentally unchanged.”
“Reform” proposals designed to “make the system prettier and more politically palatable… while leaving the system fundamentally unchanged.”
Journalists seeking to report on the web of government surveillance have found themselves harassed, monitored, and exiled from their home countries.

Journalists seeking to report on the web of government surveillance have found themselves harassed, monitored, and exiled from their home countries.
Wikileaks released documents of U.S. secret negotiations over the Trans-Pacific Partnership Agreement.

Wikileaks released documents of U.S. secret negotiations over the Trans-Pacific Partnership Agreement.
Aaron Swartz’s private whistleblower application offers anonymity and security to potential leakers.

Aaron Swartz’s private whistleblower application offers anonymity and security to potential leakers.

